
CINDER (Pt. 2): Turning Insight Into Action — The Controls, Cadence, and Evidence That Work
CINDER becomes operational: each behavior is paired with fast tests, corrective moves, and mapped controls, supported by a weekly–monthly–quarterly rhythm and a 90‑day plan that aligns CSF, 800‑171, AS9100, and SCF into durable, human‑centered security.
Complacency. Ignorance. Neglect. Drift. Evasion. Resistance.
CINDER isn’t malice. It’s human. It spreads when leaders stop watching. You beat it with clarity, cadence, and controls that people can actually use.
Below is the model, written for execs and operators who need to move now:
C — Complacency
"Nothing bad has happened, so we’re fine."
What it looks like
- Policy exists. No one can explain the why.
- Metrics don’t move. Findings roll over quarter after quarter.
Fast tests
- Ask three managers: "Name our top 3 risks and the control that contains each."
- Pull your weekly dashboard. Any leading indicators, or just lagging ones?
Moves that work
- Publish two numbers weekly: open risks and time to close.
- Tie every top risk to a visible owner and a single control.
- Put checks where the work happens. No "audit theater."
Framework alignments
- National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF) 2.0: Put Govern at the center: roles, risk strategy, policy, and oversight. Make those outcomes part of the exec agenda.
- NIST 800-171r3: Use the Assessment, Authorization & Monitoring family to keep leadership eyes on status; adopt 800-171A r3 procedures for real assessment evidence.
- AS9100 Rev D: Lean on leadership, planning, and risk‑based thinking across the Quality Management System (QMS); executives own the cadence.
- Secure Controls Framework (SCF): Stand up GOV (governance), CPL (compliance), and MON (continuous monitoring) domains for continuous, defensible signals.
Why it works
CSF 2.0 reframed security as governance plus operations; 800-171r3 and AS9100 push continuous oversight; SCF gives you common language controls and mappings to keep the board, quality, and security in sync.
I — Ignorance
Not dumb. Not trained to act.
What it looks like
- Annual slide decks. Zero behavior change.
- New hires learn security from a teammate, not the system.
Fast tests
- Five‑minute drill: "Show me how you report a suspected phish."
- Pull completion vs. comprehension: who passed, and who can perform?
Moves that work
- Replace once‑a‑year lectures with role‑based microlessons tied to job tasks.
- Trigger on events: new role, new system, new incident lessons learned.
- Measure task performance, not just attendance.
Framework alignments
- CSF 2.0: Govern roles and accountability; then Protect with awareness outcomes that tie to actual duties.
- 800-171r3: Apply Awareness & Training requirements and assess with 800171A r3; use the families list to scope by role.
- AS9100 Rev D: QMS requires competence and awareness integrated with process performance and product safety.
- SCF: Map curriculum to GOV, CPL, DCH (data handling), and PRI (privacy) domains so staff practice the exact controls they own.
Why it works
800-171r3’s outcomes and 171A’s assessment procedures make "show me" training measurable. CSF and SCF translate that into governance and control objectives your auditors and prime contractors accept.
N — Neglect
The slow rot. "I’ll get to it."
What it looks like
- Plan of Action and Milestone (POA&M) items that never die.
- "Temporary" exceptions that hit their second birthday.
Fast tests
- Pull your POA&M. Count items older than 90 days.
- Check exception inventory. How many have a sunset date?
Moves that work
- Create a monthly POA&M board. Close or escalate—no purgatory.
- Tie remediation of Service-Level Agreements (SLAs) to risk impact.
- Publish wins. People copy what you celebrate.
Framework alignments
- CSF 2.0: Use Govern → Oversight outcomes to drive closure; connect to Detect/Respond metrics so drift and debt are visible.
- 800-171r3: Treat remediation and monitoring as part of your Assessment, Authorization & Monitoring family; verify with 171A’s procedures.
- AS9100 Rev D: Use the Corrective Action Preventative Action (CAPA) mindset and risk‑based planning to eliminate recurring nonconformities. This is QMS muscle.
- SCF: Run CPL (compliance) with MON and RSK (risk) controls; they come pre‑mapped to many laws and standards to reduce audit fatigue.
Why it works
POA&M discipline plus QMS CAPA stops the slow leak. SCF gives you a control‑by‑control evidence plan.
D — Drift
Process quietly slides off spec.
What it looks like
- "We tweaked the steps. It’s faster."
- Change logs that don’t match reality.
Fast tests
- Pick one system. Compare the documented baseline to what’s deployed.
- Sample 10 changes. How many fully approved? How many emergency "after the fact?"
Moves that work
- Freeze the baseline, then run a strict, fast change path.
- Embed microaudits in the workflow. Two clicks, no blame.
- Roll back fast. Make rollbacks normal.
Framework alignments
- CSF 2.0: Protect through configuration and change outcomes; monitor under Detect; govern exceptions.
- 800-171r3: Apply Configuration Management and System & Information Integrity requirements to keep truth in sync with production.
- AS9100 Rev D: Treat it like configuration management and operational control. Risk based, controlled, traceable.
- SCF: Use CFG (configuration), CHG (change), MON (monitoring) domains to stop drift at the source.
Why it works
These frameworks all reward one idea: pick a baseline, control changes, watch constantly.
E — Evasion
People know the rule. They work around it.
What it looks like
- Shadow Software‑as‑a‑Service (SaaS). Bring Your Own (BYO) everything.
- Personal email or cloud to "get the job done."
Fast tests
- Compare finance invoices to IT’s app inventory.
- Scan for unsanctioned cloud domains and OAuth grants.
Moves that work
- Make the right path easier than the workaround.
- Sanction alternatives with better User Experience (UX).
- Inventory everything. Kill what you cannot see or govern.
Framework alignments
- CSF 2.0: Govern supply chain and third‑party use; identify assets; protect access; detect anomalies.
- 800-171r3: Lock down Access Control, Identification & Authentication, System & Communications Protection, and Configuration Management for third party and personal systems that touch Controlled Unclassified Information (CUI).
- AS9100 Rev D: Use supplier control and process discipline to keep product safety and traceability intact even when tools change.
- SCF: Turn on AST (asset), CLD (cloud), DCH (data handling), RSK (risk) controls; SCF’s mappings help you show equivalence to other standards.
Why it works
Evasion is mostly friction. Reduce it. Govern the rest. Track everything.
R — Resistance
The pushback. Treat it as data.
What it looks like
- "Security slows us down."
- Leaders nod in meetings, stall in delivery.
Fast tests
- Who wasn’t in the room when you designed the change?
- What Key Performance Indicator (KPI) will go up when they comply? Can they see it?
Moves that work
- Put the resistors in the design room. Make them co‑owners.
- Tie control adoption to outcomes they already measure.
- Celebrate speed wins that keep risk flat.
Framework alignments
- CSF 2.0 Govern: clarify roles, authorities, and risk appetite. Make accountability explicit.
- 800-171r3: Use Planning and Risk Assessment families to ground the change in documented risk and required outcomes, then assess with 171A.
- AS9100 Rev D: Leadership and risk‑based thinking are baked in; use them to align QMS, schedule, and cost to security asks.
- SCF: Map objections to specific SCF controls, then show one‑to‑many mappings to customer and regulatory asks. This is how you get buy‑in.
Mapping Matrix (CINDER → CSF 2.0, 800171r3, AS9100, SCF)
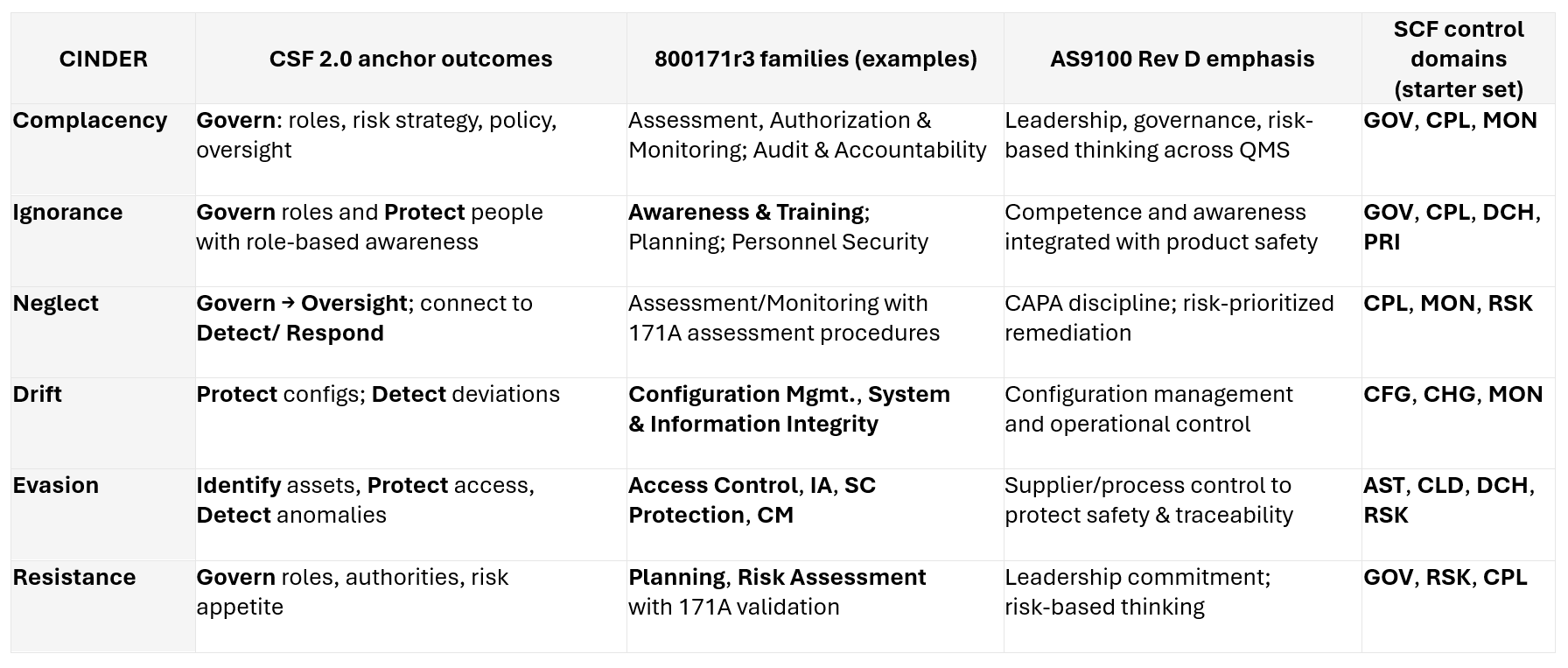
Notes: CSF 2.0 adds a dedicated Govern function and expands scope beyond critical infrastructure; 800-171r3 (May 14, 2024) realigns requirements to 800-53r5 with clearer outcomes and 171A r3 assessment procedures; AS9100 Rev D embeds risk‑based thinking throughout QMS and requires leadership ownership; SCF normalizes requirements into a common control language with transparent mappings.
Operating rhythm that satisfies all four frameworks
Weekly
- 15‑minute risk standup (top 5 risks, actions, owners).
- One baseline drift check (rotate systems).
- One role‑based microlesson tied to a real task.
Monthly
- POA&M board: close or escalate.
- Audit trail spot check with an insight to leadership.
- Change board: fast, strict, traceable.
Quarterly
- Baseline reviews for critical systems.
- Shadow IT and asset inventory sweep.
- Tabletop on a high‑impact scenario.
This rhythm bakes CSF Govern into leadership cadence, keeps 800-171 outcomes assessed and evidenced, maintains AS9100 discipline for change and nonconformity, and ties your day-to-day to SCF controls that cross map to everything your customers and auditors ask for.
Implementation guide: 90 days
Phase 1: Set the frame (Weeks 1–3)
- Approve CSF Govern outcomes, risk appetite, and roles. Publish them.
- Baseline your 800-171r3 posture using the 171A r3 assessment procedures; capture evidence as you go.
- Lock AS9100 ownership for configuration, change, and CAPA.
- Stand up SCF GOV/CPL/MON controls as your minimal viable backbone.
Phase 2: Control the work (Weeks 4–8)
- Freeze baselines on one critical system; require change approvals; implement drift checks. (CSF Protect/Detect, 800-171 CM/SI, AS9100 operational control, SCF CFG/CHG/MON.)
- Launch microlessons tied to top risks and roles; verify with quick drills (171A).
- Start the POA&M board; track SLA breaches; publish closures (CSF Govern → Oversight).
Phase 3: Make it durable (Weeks 9–12)
- Expand baselines to two more systems; automate monitoring where possible. (SCF MON; CSF Detect.)
- Integrate supplier controls and third‑party use (AS9100 supply chain focus; 800-171 AC/IA/SCP; SCF AST/CLD/DCH).
- Publish an exec dashboard that speaks CSF outcomes and shows 800-171/AS9100/SCF evidence behind every metric.
Evidence strategy (what auditors and primes want to see)
- CSF 2.0: show Govern artifacts (charter, roles, risk appetite), outcome metrics, and continuous oversight.
- 800-171r3: map each requirement to 171A r3 procedures and retain artifacts per control-configs, logs, tickets, training performance, and POA&M entries.
- AS9100 Rev D: demonstrate leadership commitment, risk assessments, configuration and change discipline, CAPA closure, and supplier control records.
- SCF: show your Statement of Applicability and control tailoring; use SCF’s cross mappings to demonstrate equivalence for customers who speak different frameworks.
Appendix: Fast crosswalk examples (expandable)
CINDER: Drift
- 800-171r3: Configuration Management (e.g., baseline, change control), System & Information Integrity (monitoring) → assessed via 171A r3.
- AS9100: Clause 8 operational control and configuration management disciplines.
- SCF: CFG, CHG, MON controls (pre‑mapped across frameworks).
CINDER: Evasion
- 800-171r3: AC/IA/SCP/CM families for third party and personal system use around CUI.
- AS9100: Supplier and process control for traceability and product safety.
- SCF: AST (asset), CLD (cloud), DCH (data handling), RSK (risk).
CINDER: Neglect
- 800-171r3 + 171A r3 for assessment rigor and living POA&M; link to exec oversight under CSF Govern.
- AS9100 CAPA closes the loop.
- SCF CPL + MON drive repeatable evidence.
Why this is credible
- CSF 2.0 (Feb 2024) made Govern a core function and expanded applicability to all orgs, giving you an executive friendly taxonomy.
- 800-171r3 (May 14, 2024) finalized streamlined, outcome‑oriented requirements aligned to 80053r5, with 171A r3 assessment procedures to standardize evidence.
- AS9100 Rev D (aligned to ISO 9001:2015) embeds risk‑based thinking, configuration control, supplier management, and leadership accountability for aerospace—exactly where CINDER bites.
- SCF provides ~1,400+ controls across 33 domains, transparent mappings, and guidance to normalize compliance while improving security operations.
Resources
- NIST Cybersecurity Framework
- NIST CSF Tools
- NIST Computer Security Resource Center
- International Aerospace Quality Group (IAQG) – 9100 Quality Management Systems
- Secure Controls Framework (SCF)
- SCF Control Reference
- NIST SP 800‑171Ar3
- National Quality Assurance (NQA) – Aerospace Management AS9100
Related Insights

CINDER (Pt. 1): The Human Behaviors That Quietly Erode Security Programs
CINDER identifies predictable human behaviors that undermine security and positions governance, clarity, and evidence‑driven systems as the foundation for preventing routine work pressures from turning into structural security failures.

Security Playbook: A CISO's Guide to NIST Governance
A playbook for CISOs to run governance as a system. Align CSF 2.0 and RMF with SP 800‑53/55/137 and BCEB, set decision forums, and execute a 90‑day plan to prove, monitor, and improve controls.

Resilience in the Age of Permacrisis
The concept of 'permacrisis' describes our new reality of overlapping emergencies. We present a new framework for organizational resilience that moves beyond risk management to embrace strategic redundancy, decentralized decision-making, and anti-fragility.
Ready to deepen your strategy?
Obsidian Rowe partners with leaders to navigate the complexities discussed in this article.
Start a Conversation
